A soc dashboard is the operational layer that turns security data into decisions. For SOC managers, analysts, and incident responders, its business value is simple: faster detection, smarter prioritization, cleaner handoffs, and more consistent response under pressure.
Without a well-designed dashboard, teams bounce between SIEM searches, EDR consoles, ticketing queues, email threads, and spreadsheets. That fragmentation creates alert fatigue, slows investigations, and makes it hard to answer basic questions like:
A strong soc dashboard solves those problems by centralizing risk signals, workflow status, and performance metrics into role-specific views that support action, not just observation.
A soc dashboard is a visual command center for security operations. It consolidates telemetry, alerts, case data, and operational metrics so security teams can monitor threats, triage incidents, and measure response performance in real time.
In daily operations, the dashboard helps analysts quickly identify what changed, what matters, and what should be worked first. Instead of manually collecting context from multiple tools, they can see alert patterns, asset criticality, user activity, investigation status, and team workload in one place.
This matters because the SOC rarely fails from lack of data. It fails from lack of clarity. Most teams already have logs, detections, and alerts. The challenge is turning that volume into a usable operating picture.
A practical soc dashboard helps teams:
These terms are often used interchangeably, but they serve different purposes.
SOC dashboard
SIEM console
Reporting view
A mature SOC uses all three. The dashboard sits in the middle, translating technical activity into operational awareness.
If your soc dashboard tracks everything, it helps with nothing. The right approach is to focus on metrics that improve prioritization, response speed, team efficiency, and risk visibility.
These are the baseline health indicators for any soc dashboard. Alert volume shows whether the environment is stable or flooding. Severity distribution helps leaders quickly assess whether the queue is mostly routine noise or contains meaningful risk. Detection trends show whether spikes are isolated events, seasonal patterns, or signals of deteriorating defenses.
The key is context. A spike in alerts is not automatically bad if it comes from a newly deployed detection rule that is working as intended. Likewise, low alert volume is not automatically good if detections are broken or logs are missing.
These metrics tell you whether the SOC is moving quickly enough. MTTD reflects monitoring effectiveness. MTTR reflects operational discipline. Escalation rate shows whether junior analysts can resolve issues independently or whether too much work is being pushed upward.
Together, they answer a strategic question: is the SOC merely observing threats, or actually managing them efficiently?
These metrics determine sustainability. High false positive rates drain time. Low closure rates signal backlog growth. Poor workload distribution leads to burnout, slow handoffs, and inconsistent case quality.
A strong soc dashboard should make these operational constraints visible before they become staffing or service-level failures.
Prioritization improves when alerts are tied to business context. A medium-severity alert on a domain controller or privileged admin account may deserve faster attention than a higher-volume issue on a low-value test system.
Exposure indicators help teams answer:
That is how dashboards move from technical reporting to risk-based security operations.
A single all-purpose soc dashboard usually fails because different roles need different levels of detail. The better model is a set of purpose-built views connected by drill-down paths.
The executive view should translate technical activity into posture and business impact. It is not for active triage. It is for leadership alignment, investment discussions, and risk communication.
This view should emphasize:
Executives do not need raw event lists. They need concise answers about whether security risk is rising, where controls are under stress, and whether the SOC is operating effectively.
The analyst triage view is where operational value becomes immediate. This dashboard must help an analyst answer, within seconds, what to investigate first and why.
It should include:
Once an alert becomes a case, the dashboard needs to shift from queue management to evidence correlation. Investigation views should connect timeline, entities, detections, and actions in one workspace.
Critical components include:
This view is for managers, shift leads, and team coordinators. It focuses less on threat details and more on service delivery and operational control.
It should track:
A successful soc dashboard is not built by asking what data is available. It is built by asking what decisions each role must make, then surfacing the minimum information required to make those decisions well.
Begin with the users:
If one dashboard tries to satisfy all four audiences equally, it usually satisfies none of them.
Use chart types based on actionability:
Avoid decorative visuals that look polished but add no operational value. In a SOC, clarity beats creativity.
Security data is sensitive. Your soc dashboard should support role-based access so executives see posture without case-level evidence, while analysts and responders can drill into the detail they need.
Drill-downs matter because no summary metric is enough on its own. Users should be able to move from high-level KPIs to cases, entities, and underlying events without losing context.
Workflow context matters just as much. Dashboards should not stop at “what happened.” They should also show “what is assigned,” “what is blocked,” and “what happens next.”
The most common failures in soc dashboard design are predictable:
A dashboard should help people decide, prioritize, and act. If it only informs passively, it is underperforming.
The real test of a soc dashboard is whether it improves actual workflows. If it cannot accelerate triage, simplify investigations, and support continuous improvement, it is just a display layer.
The first workflow is deciding what deserves immediate attention. Good dashboards reduce noise and elevate the alerts most likely to matter.
To support triage well, the dashboard should:
A mature dashboard supports containment by showing:
This reduces response friction and helps teams move from detection to containment with fewer handoff delays.
Review these areas regularly:
That feedback loop is what turns a dashboard from an operational monitor into a management system.
From a consulting perspective, the best implementations are iterative, use-case-led, and tightly mapped to operational workflows.
Start with concrete questions:
Then map each question to a KPI or view. This prevents dashboard sprawl.
A soc dashboard is only as useful as the consistency of its inputs. Normalize log fields, severity labels, asset identifiers, and user attributes. Enrich alerts with asset criticality, identity context, threat intelligence, and ownership metadata before visualizing them.
Without enrichment, dashboards become fast-looking but shallow.
Build separate views for executives, managers, analysts, and responders. Then connect them through drill-downs so each user can move deeper only when needed.
This gives every stakeholder the right level of visibility without exposing unnecessary complexity.
SOC metrics decay. Rules change. Volume shifts. Teams mature. Reassess your core dashboard metrics regularly to ensure they still reflect useful operational truth.
Retire metrics that no longer drive action. Add ones tied to emerging workflows or control gaps.
The dashboard should evolve alongside detections, playbooks, and staffing models. When analysts struggle, the fix may be more than rule tuning. It may be a visibility and workflow design problem.
Designing a high-value soc dashboard manually is possible, but it is rarely efficient. Most teams end up stitching together SIEM exports, spreadsheets, ticketing data, and custom visual layers. That approach is slow to build, hard to maintain, and difficult to scale across roles.
This is where FineBI becomes the practical enabler.
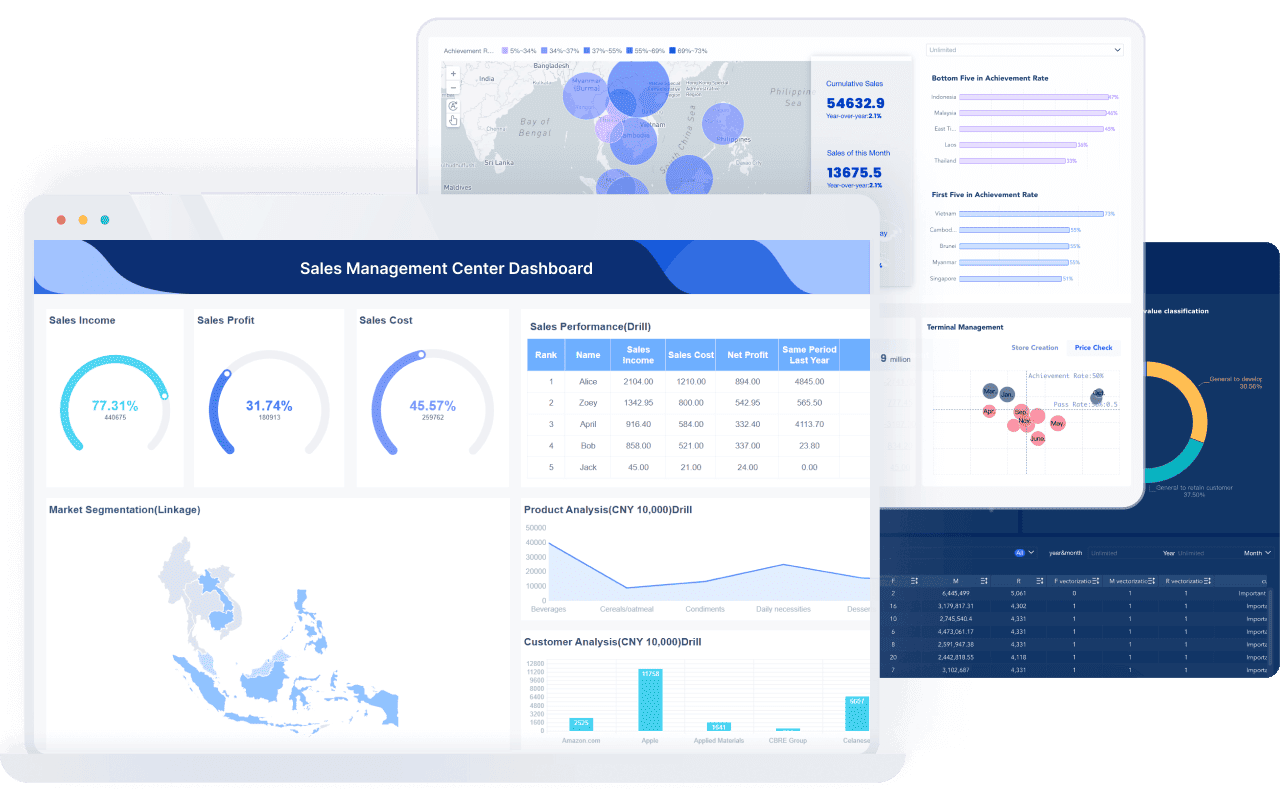
Building this manually is complex; use FineBI to utilize ready-made templates and automate this entire workflow. Instead of assembling fragmented reporting logic from scratch, teams can use FineBI to:
 Utilize ready-made templates and automate this entire workflow with FineBI
Utilize ready-made templates and automate this entire workflow with FineBI
For enterprise decision-makers, the value is not just prettier visualization. It is faster deployment, stronger consistency, and lower operational overhead. For security teams, it means less time building dashboards and more time improving detection, triage, and response.
If your current soc dashboard depends on manual reporting work, disconnected tools, or one-off analyst effort, that is the signal to modernize. FineBI helps turn SOC data into a repeatable, scalable decision system.
A SOC dashboard gives security teams a real-time view of alerts, incidents, KPIs, and workflow status in one place. Its main purpose is to help analysts and managers detect threats faster, prioritize better, and coordinate response more efficiently.
A practical SOC dashboard should focus on metrics like alert volume, severity distribution, MTTD, MTTR, false positive rate, escalation rate, and case closure rate. These KPIs help teams measure risk, response speed, and operational efficiency without overwhelming users with noise.
A SIEM is the underlying system for collecting logs, correlating events, and supporting deep investigation, while a SOC dashboard is the visibility layer built for quick decision-making. The dashboard summarizes what matters now, whereas the SIEM usually provides more raw technical detail.
SOC analysts, incident responders, managers, and executives can all use a SOC dashboard, but each role needs a different view. Analysts need actionable alert and case context, while leaders need trend, workload, and performance summaries.
An effective SOC dashboard highlights high-priority risks, reduces manual tool switching, and shows both current threats and team performance clearly. It should be role-based, easy to interpret, and tied directly to investigation and response workflows.

The Author
Lewis Chou
Senior Data Analyst at FanRuan
Related Articles

Payment Analytics Dashboard: 12 KPIs Every Operations Leader Should Track to Cut Revenue Leakage
Losing revenue to declines? Discover 12 essential KPIs to track in your payment analytics dashboard to stop leakage and manage disputes.
Lewis Chou
May 05, 2026
EMR Dashboard Guide: 12 Metrics to Track for Faster Clinical and Operational Decisions
Learn the 12 essential EMR dashboard metrics to track for faster clinical and operational decisions, improving patient flow and revenue cycle management.
Lewis Chou
May 05, 2026
Talent Acquisition Dashboard: A Scenario-Based Guide to Faster, Better Hiring Decisions
Learn how a talent acquisition dashboard provides a decision-ready view to identify hiring bottlenecks, improve candidate quality, and accelerate recruitment.
Lewis Chou
May 05, 2026