A ciso dashboard should help executives make better decisions about risk, investment, resilience, and accountability. Yet in many organizations, security leaders still present dashboards that are too technical, too crowded, or too disconnected from business priorities to influence action.
If you are a CISO, CIO, VP of Security, IT director, or risk leader, the problem is familiar: leadership wants clarity, not a data dump. They need to know what changed, what matters now, where the business is exposed, and what decisions are required this month or quarter. A dashboard that fails to answer those questions quickly will be ignored.
This guide explains how to design a ciso dashboard that executives actually use, what metrics matter most, how to structure the view for fast decision-making, and how to avoid the common reporting mistakes that destroy trust.
The biggest reason a ciso dashboard fails is simple: most security reporting is built around what security teams can measure, not what executives need to decide.
Security teams naturally gravitate toward operational data: alert counts, scan results, severity distributions, patch volumes, or tool-specific outputs. But executives are not trying to run the SOC. They are trying to understand whether cyber risk is rising or falling, whether the organization is adequately protected, and whether management is taking the right actions.
When a dashboard leans too far into technical detail, three problems appear fast:
Executives also lose trust when the dashboard feels static or disconnected from business context. Reporting that says “35 critical vulnerabilities remain open” is incomplete. Reporting that says “35 critical vulnerabilities remain open across two revenue-critical applications, both outside policy threshold, owned by the digital commerce and infrastructure teams, with remediation due in 14 days” is actionable.
What leaders actually need from a ciso dashboard is much narrower and much more strategic:
If the dashboard does not answer those four questions in minutes, executives will stop using it.
A strong ciso dashboard is not just a status screen. It is a decision-support tool for leadership.
Its purpose is to help executives govern cyber risk in business terms. That means translating security posture into signals that support strategic oversight, budget prioritization, compliance readiness, and cross-functional accountability.
Used properly, the dashboard should help leadership:
This is why the best ciso dashboard is tied directly to a short list of recurring executive decisions. For most organizations, those decisions include:
A CISO cybersecurity dashboard is an executive-level reporting view that brings together security, risk, identity, exposure, and compliance indicators into a clear picture of organizational cyber posture.
Its value is not in showing every available security metric. Its value is in making risk visible, showing movement over time, and pointing leaders toward specific actions.
It is different from operational SOC reporting or analyst dashboards in a few important ways:
In other words, a SOC analyst may need to know which alerts fired in the last four hours. An executive needs to know whether incident frequency is increasing in a business-critical environment and whether response capability is performing within target.
Below is a practical KPI set for a ciso dashboard. Not every organization needs all of them, but every metric should support a decision.
A useful rule: if a metric cannot trigger a discussion, a decision, or an action, it likely does not belong on the executive page.
The most effective ciso dashboard starts with decision design, not data collection.
Before choosing a single metric, list the decisions executives need to make on a monthly or quarterly basis. For example:
Then map each metric to a business question. If the metric does not help answer a question leaders care about, exclude it.
Consultant best practice: run a short stakeholder workshop with the CEO, CFO, CIO, legal, compliance, and major business unit leaders. Ask what they need to know, what they routinely ask for, and what would cause them to intervene. Build your first dashboard around those answers.
Executives do not need exhaustive reporting. They need signal, not noise.
A better ciso dashboard emphasizes:
That means removing vanity metrics such as total blocked emails, raw alert volume, or long lists of closed tickets unless those figures directly support a strategic point.
A concise executive page often outperforms a sophisticated but overloaded one. In most cases, one page with 6 to 10 high-value indicators is enough.
Ask this question for every metric: Would leadership make a different decision if this number changed? If the answer is no, cut it.
Security metrics become meaningful to executives when they are connected to consequences.
Do not stop at reporting incidents, vulnerabilities, or control gaps. Explain what they could mean for the business:
For example, instead of saying “privileged access review completion dropped to 71%,” say “privileged access review completion dropped to 71%, increasing the risk of unauthorized access across finance and ERP systems before quarter close.”
Use plain language. Avoid writing as if the dashboard is intended for practitioners only. If a non-technical executive cannot scan a note and understand the impact in seconds, rewrite it.
Identity is now one of the most important executive-level risk domains, yet many ciso dashboard designs still underrepresent it.
That is a mistake. Modern attacks often exploit credentials, excessive privileges, stale accounts, third-party access, and weak identity governance before they exploit deeper technical weaknesses.
Make identity and access posture visible with indicators such as:
This matters because identity failures often have direct enterprise consequences. When executives can see access governance clearly, they can support policy enforcement, resourcing, and remediation across functions, not just inside security.
Raw numbers rarely tell leaders whether something is acceptable.
A ciso dashboard should show:
For example, “12 open critical findings” has limited value by itself. But “12 open critical findings, up from 7 last month, above threshold of 5, concentrated in two customer-facing applications” immediately communicates urgency.
Thresholds help executives focus. Trendlines help them judge progress. Together, they make it obvious where attention is needed now.
Use red, yellow, and green sparingly and consistently. A good rule is to reserve color for conditions tied to a defined threshold, not for decoration.
Compliance updates often become separate slide decks because leadership cannot quickly see audit readiness in the main dashboard.
A better approach is to make compliance visible in the ciso dashboard itself. Summarize:
This gives executives a single view of whether the organization is on track or drifting toward an avoidable compliance issue.
It also reduces reporting duplication across security, compliance, internal audit, and risk teams. Instead of rebuilding the same update repeatedly, leadership gets a live, shared view of posture and progress.
One of the most common dashboard design failures is trying to satisfy every audience with one page.
That approach does not scale. Executives need a concise strategic view. Security managers need operational detail. Analysts need technical drill-downs.
The right model is layered reporting:
This structure prevents executive meetings from being pulled into tactical detail while still allowing leaders to drill down when needed.
Think of the executive dashboard as the front door, not the entire building.
A dashboard without ownership creates awareness without action.
Every item marked red or yellow should include:
This turns the ciso dashboard into an operating mechanism for accountability. It also helps executives distinguish between known, managed risks and unmanaged drift.
A practical executive annotation might look like this:
That level of clarity changes the conversation from “What is happening?” to “Are we on track?”
No ciso dashboard is perfect on the first version. The only reliable way to improve adoption is to watch how leaders actually use it.
Test the dashboard with real stakeholders and ask:
Then refine the wording, layout, thresholds, and annotations based on actual usage patterns, not internal assumptions.
Consultant best practice: track dashboard engagement over a few reporting cycles. If executives consistently skip a section or ask for the same clarification repeatedly, redesign that part. Executive reporting should evolve with the business, not remain fixed.
A ciso dashboard works best when it follows a simple, repeatable layout. Executives should be able to open the page and know exactly where to look first.
A practical structure looks like this:
This order mirrors how leadership consumes information: overall status first, then material concerns, then direction, then obligations, then actions.
Start with a compact summary of current cyber posture. This should communicate the overall state in one glance.
Include:
Use scorecards or a concise summary table here. Keep it high level.
This section should focus only on incidents or exposure shifts with executive relevance.
Include:
A short annotated table often works better than multiple charts. The key is context: what happened, what it affected, and what management is doing next.
Because identity is a high-frequency attack path and a common control weakness, give it dedicated space.
Include:
A scorecard plus one trendline is often enough for the executive view.
This section should summarize audit readiness and control health without becoming a checklist.
Include:
Heatmaps can be useful here if they are simple and clearly labeled. If the heatmap requires explanation, it is too complex for the top page.
End with the most important operational governance block: what leaders need to approve, support, or escalate.
Include:
This is where the dashboard becomes a tool for executive action, not just awareness.
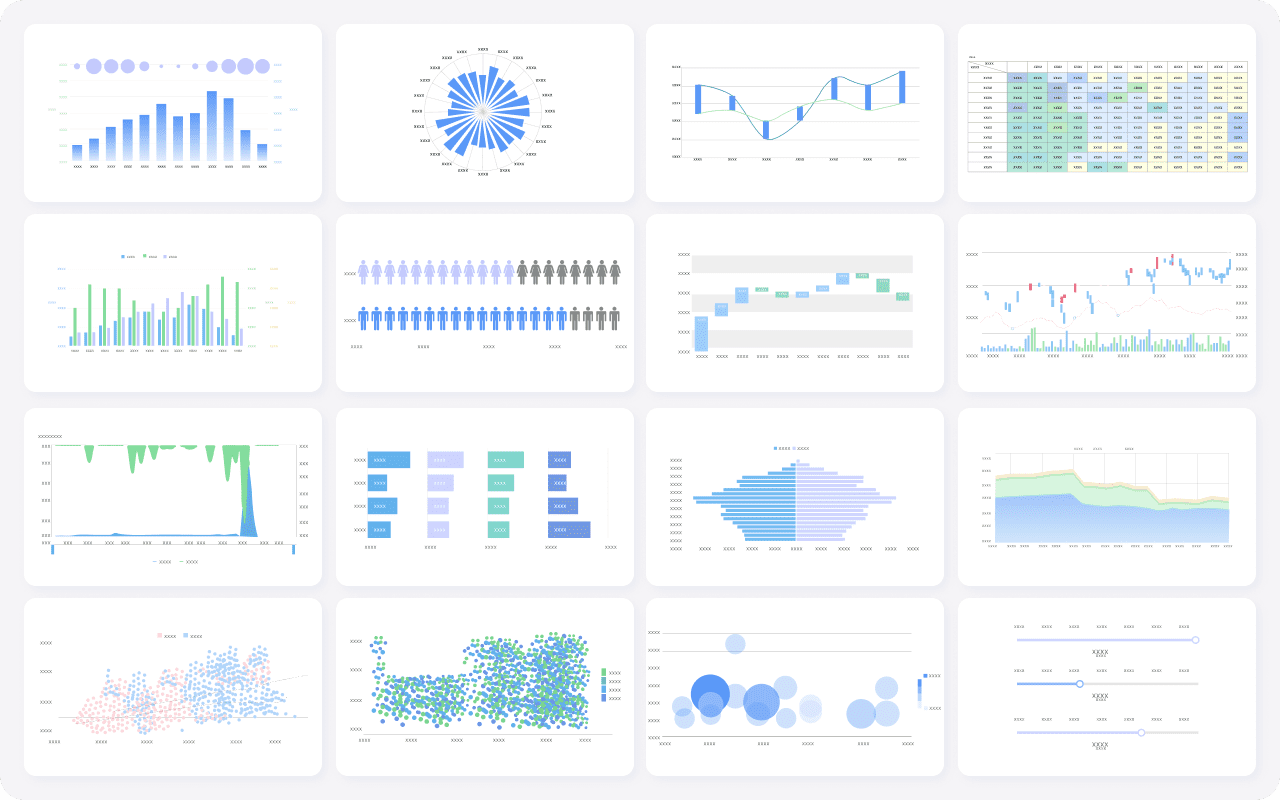
Different visual forms serve different purposes. Choose the one that makes the point fastest.
Do not over-visualize. In executive settings, one clear table often beats four decorative charts.
Even mature organizations fall into predictable traps when building a ciso dashboard.
Analyst dashboards are designed for investigation and control execution. Executives need synthesis, prioritization, and implications. Reusing operational layouts creates confusion and weakens executive engagement.
More charts do not create more value. Without a clear story, the dashboard becomes a collage of activity. Each section should answer a specific question and point toward a decision.
A red indicator alone is not enough. Leaders need to know what caused it, who owns it, and what happens next. Otherwise the report triggers concern without enabling action.
As the organization grows, enters new markets, changes architecture, or adopts new regulatory obligations, old thresholds may stop reflecting material risk. Review KPI definitions regularly so the dashboard stays aligned with current business reality.
Before finalizing your ciso dashboard, run this checklist:
If you cannot answer yes to most of these, the dashboard is probably still too operational.
Designing an executive-ready ciso dashboard manually is possible, but it is rarely efficient. You have to unify data from security tools, compliance systems, IAM platforms, spreadsheets, and business records, then maintain layout logic, drill-downs, thresholds, and update cycles. That complexity is exactly why many dashboard efforts stall or become stale.
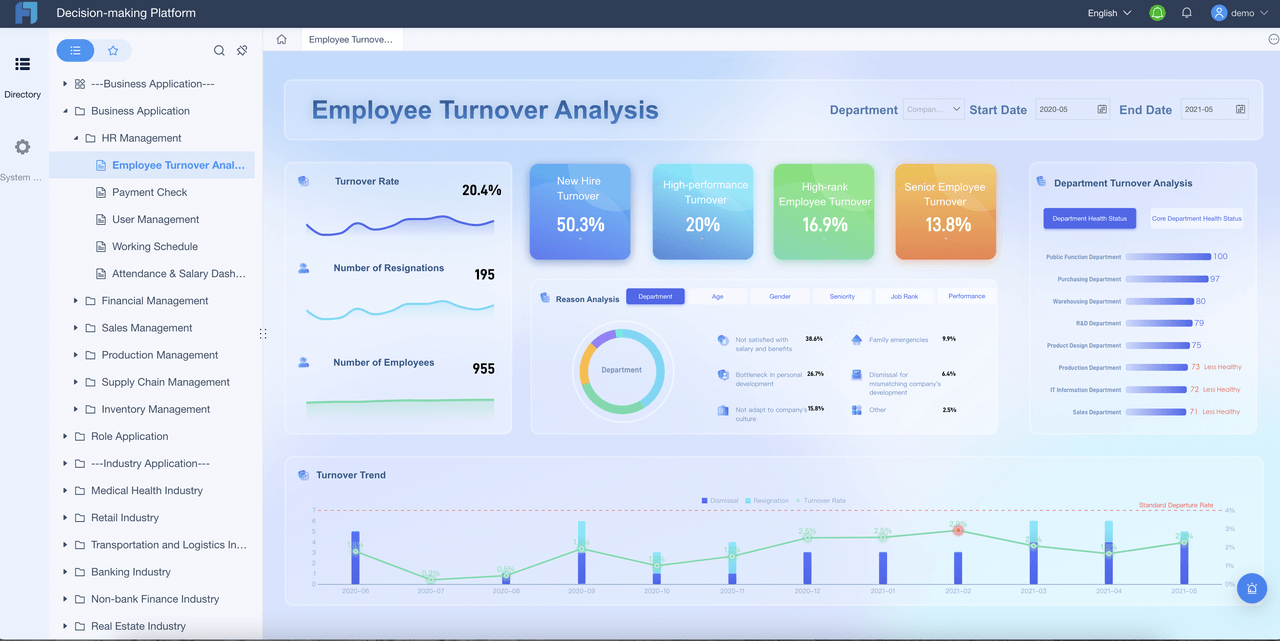
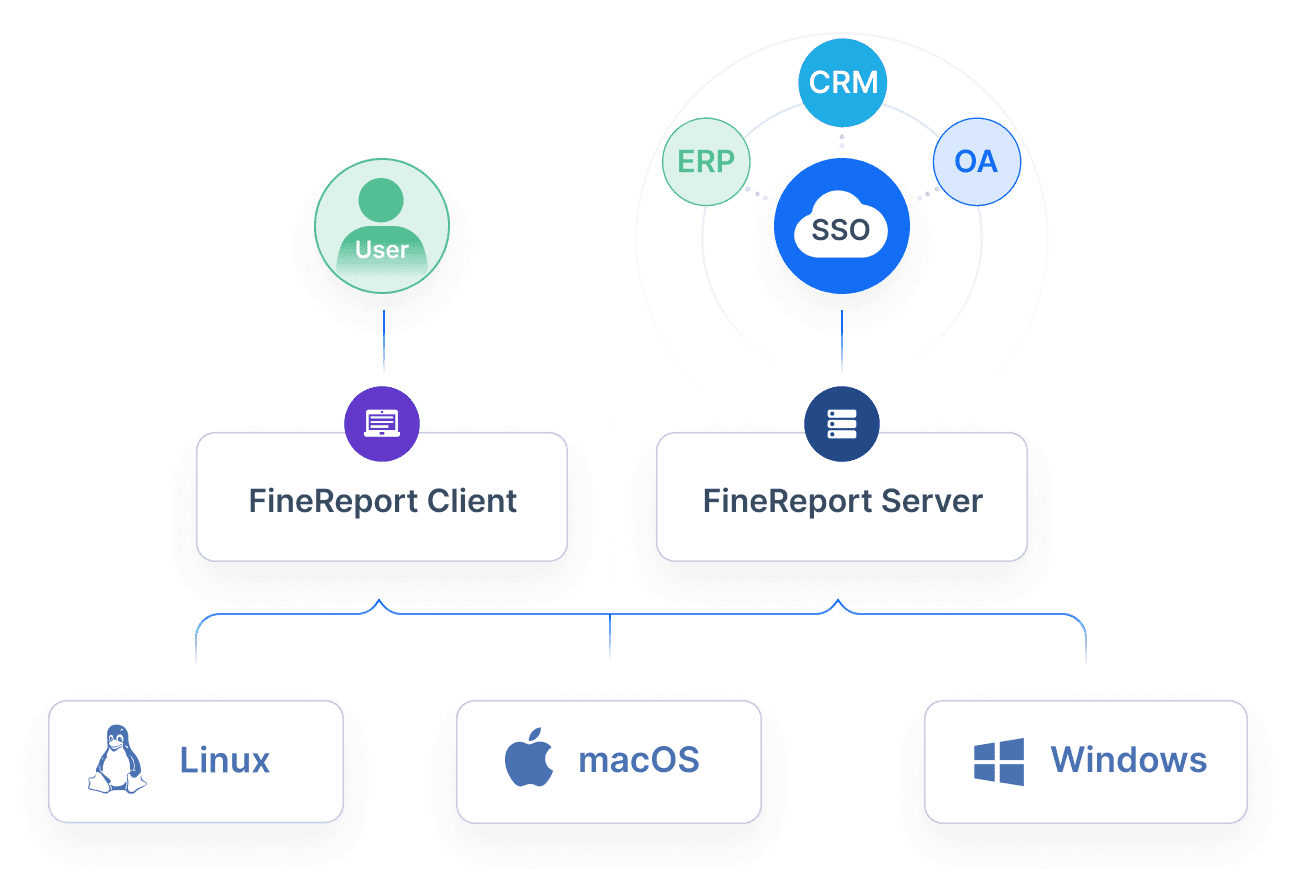
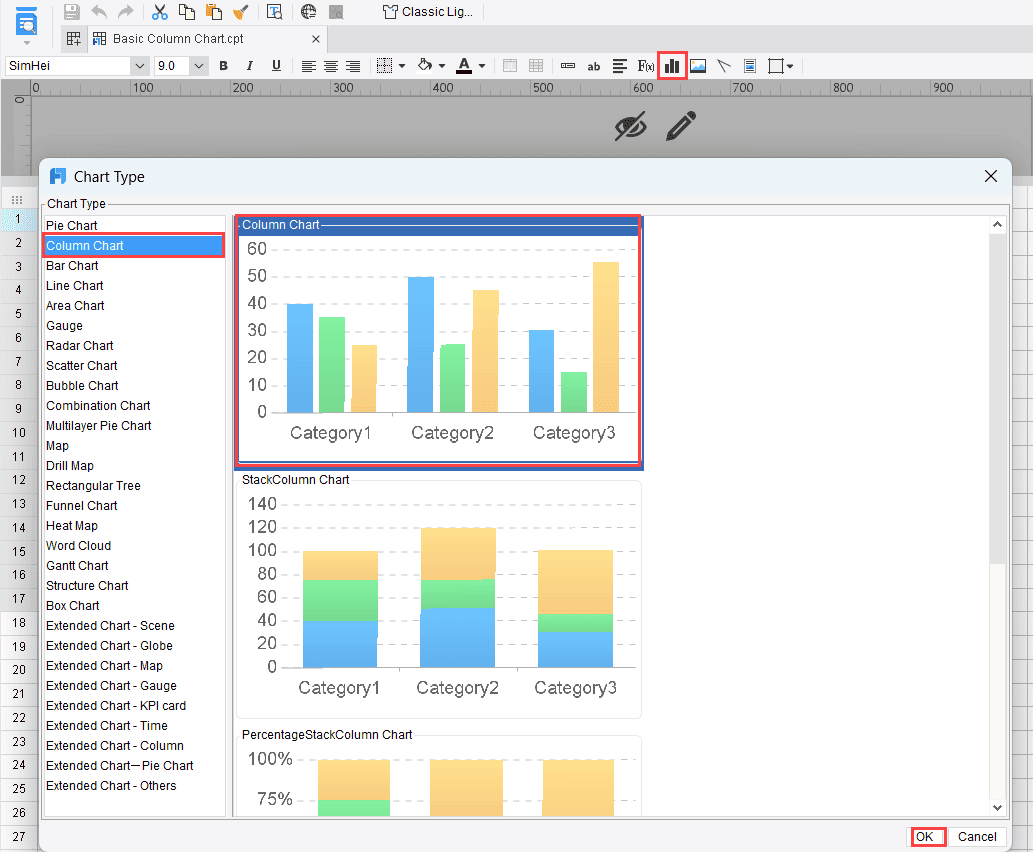
Building this manually is complex; use FineReport to utilize ready-made templates and automate this entire workflow.
FineReport helps security and risk leaders turn fragmented reporting into a structured executive dashboard that is easier to maintain and easier for leadership to trust. With FineReport, teams can:
For enterprise teams, that means less time assembling reports and more time driving action. Instead of rebuilding the same ciso dashboard every reporting cycle, you can create a repeatable system that supports leadership oversight, compliance reporting, and risk accountability at scale.
If your goal is to create a ciso dashboard executives actually use, the winning formula is clear: fewer metrics, better business context, visible ownership, and a platform that makes the process sustainable. FineReport gives you the structure and automation to make that happen.
It should show the top risks, their business impact, whether exposure is improving or worsening, and what decisions or escalations are needed. If leaders cannot grasp those points quickly, the dashboard is unlikely to drive action.
A CISO dashboard is built for executive oversight, risk governance, and investment decisions. A SOC dashboard is more operational and focuses on alerts, investigations, and analyst workload.
The most useful metrics are enterprise risk posture, risk trend, material incidents, MTTD, MTTR, critical vulnerability exposure, compliance status, and remediation ownership. The right set depends on which decisions leadership needs to make regularly.
They usually fail because they are too technical, too crowded, or disconnected from business priorities. Trust also drops when metrics lack context, trend data, or clear ownership for remediation.
It should be updated often enough to reflect meaningful change, typically monthly for executives and quarterly for boards, with faster refreshes for major incidents or material risks. The key is keeping the data timely, consistent, and decision-ready.

The Author
Yida Yin
FanRuan Industry Solutions Expert
Related Articles

What Is a Benchmark Dashboard? Practical Guide to Compare Teams, Sites, and Time Periods
A benchmark dashboard is a decision making tool that helps operations leaders compare performance across teams, locations, and time periods in one place. Its business value is simple: it turns scattered KPIs into a fair,
Yida Yin
Jan 01, 1970

CFO Dashboard Examples: How to Build a Dashboard Executives Actually Use
Executives do not need another report. They need a decision tool. That is the real difference between weak and effective cfo $1 . A $1 should help leaders identify what changed, why it matters, and what action to take ne
Yida Yin
Jan 01, 1970

Workforce Metrics Dashboard: 9 Steps to Build One for Better Executive Decision-Making
A workforce $1 is not just an HR $1. In practice, it is an executive decision system that turns workforce data into signals leaders can act on quickly. For CHROs, CEOs, CFOs, COOs, and business unit leaders, the value is
Yida Yin
Jan 01, 1970